على غرار الإصدارات السابقة، يتضمّن Android 15 تغييرات في السلوك قد تؤثّر في تطبيقك. تنطبق تغييرات السلوك التالية حصريًا على التطبيقات التي تستهدف Android 15 أو الإصدارات الأحدث. إذا كان تطبيقك يستهدف Android 15 أو الإصدارات الأحدث، عليك تعديله ليتوافق مع هذه السلوكيات بشكلٍ صحيح، حيثما ينطبق ذلك.
احرص أيضًا على مراجعة قائمة تغييرات السلوك التي تؤثّر في جميع التطبيقات
التي تعمل على Android 15 بغض النظر عن targetSdkVersion في تطبيقك.
الوظيفة الأساسية
يعدّل Android 15 أو يوسّع إمكانات أساسية مختلفة في نظام Android.
تغييرات على الخدمات التي تعمل في المقدّمة
نحن بصدد إجراء التغييرات التالية على الخدمات التي تعمل في المقدّمة في Android 15.
- سلوك مهلة الخدمة التي تعمل في المقدّمة لمزامنة البيانات
- نوع الخدمة الجديدة التي تعمل في المقدّمة لمعالجة الوسائط
- القيود المفروضة على
BOOT_COMPLETEDمستقبلات البث التي تبدأ الخدمات التي تعمل في المقدّمة - قيود على بدء الخدمات التي تعمل في المقدّمة عندما يكون لدى التطبيق إذن
SYSTEM_ALERT_WINDOW
سلوك مهلة الخدمة التي تعمل في المقدّمة لمزامنة البيانات
يقدّم Android 15 سلوكًا جديدًا للمهلة في dataSync للتطبيقات التي تستهدف Android 15 (المستوى 35 من واجهة برمجة التطبيقات) أو الإصدارات الأحدث. ينطبق هذا السلوك أيضًا على
نوع "mediaProcessing" الجديد للخدمة التي تعمل في المقدّمة.
يسمح النظام بتشغيل خدمات dataSync للتطبيق لمدة 6 ساعات إجمالاً
خلال 24 ساعة، وبعدها يستدعي النظام طريقة
Service.onTimeout(int, int) الخاصة بالخدمة
قيد التشغيل (المتوفرة في Android
15). في هذه المرحلة، تتوفّر للخدمة بضع ثوانٍ للاتصال بالرقم
Service.stopSelf(). عند استدعاء Service.onTimeout()، لن تعود
الخدمة خدمة تعمل في المقدّمة. إذا لم تُشغِّل الخدمة Service.stopSelf()، يُرسِل النظام استثناءً داخليًا. يتم تسجيل
الاستثناء في Logcat مع الرسالة التالية:
Fatal Exception: android.app.RemoteServiceException: "A foreground service of
type dataSync did not stop within its timeout: [component name]"
لتجنُّب المشاكل المتعلّقة بهذا التغيير في السلوك، يمكنك اتّخاذ إجراء أو أكثر من الإجراءات التالية:
- يجب أن تنفِّذ خدمتك طريقة
Service.onTimeout(int, int)الجديدة. عندما يتلقّى تطبيقك المكالمة المُعاد توجيهها، احرص على الاتصال بالرقمstopSelf()في غضون بضع ثوانٍ. (إذا لم توقف التطبيق على الفور، سيُنشئ النظام حالة تعطُّل.) - تأكَّد من أنّ خدمات
dataSyncفي تطبيقك لا تعمل لأكثر من إجمالي 6 ساعات في أي فترة 24 ساعة (ما لم يتفاعل المستخدم مع التطبيق، يؤدي ذلك إلى إعادة ضبط الموقّت). - لا تبدأ
dataSyncالخدمات التي تعمل في المقدّمة إلا نتيجةً لتفاعل مباشر من العميل، لأنّ تطبيقك يكون في المقدّمة عند بدء الخدمة، ويكون لدى خدمتك ست ساعات كاملة بعد انتقال التطبيق إلى الخلفية. - بدلاً من استخدام خدمة
dataSyncتعمل في المقدّمة، استخدِم واجهة برمجة تطبيقات بديلة.
إذا استمر تشغيل خدمات dataSync التي تعمل في المقدّمة في تطبيقك لمدة 6 ساعات في آخر
24 ساعة، لا يمكنك بدء خدمة أخرى تعمل في المقدّمة dataSync ما لم ينقل المستخدم
تطبيقك إلى المقدّمة (ما يؤدي إلى إعادة ضبط الموقّت). إذا حاولت
بدء dataSync خدمة أخرى تعمل في المقدّمة، يُرسِل النظام
ForegroundServiceStartNotAllowedException
رسالة خطأ مثل "انتهت المهلة الزمنية للخدمة التي تعمل في المقدّمة
من النوع dataSync".
الاختبار
لاختبار سلوك تطبيقك، يمكنك تفعيل مهلات مزامنة البيانات حتى إذا كان تطبيقك
لا يستهدف الإصدار 15 من نظام التشغيل Android (ما دام التطبيق يعمل على جهاز
Android 15). لتفعيل المهلات، شغِّل الأمر adb التالي:
adb shell am compat enable FGS_INTRODUCE_TIME_LIMITS your-package-name
يمكنك أيضًا تعديل فترة المهلة لتسهيل اختبار سلوك
تطبيقك عند بلوغ الحدّ الأقصى. لضبط فترة مهلة جديدة، شغِّل adb الأمر التالي:
adb shell device_config put activity_manager data_sync_fgs_timeout_duration duration-in-milliseconds
نوع الخدمة الجديدة التي تعمل في المقدّمة لمعالجة الوسائط
Android 15 引入了一种新的前台服务类型 mediaProcessing。此服务类型适用于转码媒体文件等操作。例如,媒体应用可能会下载音频文件,并需要先将其转换为其他格式,然后才能播放。您可以使用 mediaProcessing 前台服务,确保即使应用在后台运行时转换也会继续。
系统允许应用的 mediaProcessing 服务在 24 小时内总共运行 6 小时,之后系统会调用正在运行的服务的 Service.onTimeout(int, int) 方法(在 Android 15 中引入)。此时,服务有几秒钟的时间来调用 Service.stopSelf()。如果服务未调用 Service.stopSelf(),系统会抛出内部异常。系统会在 Logcat 中记录此异常,并显示以下消息:
Fatal Exception: android.app.RemoteServiceException: "A foreground service of
type mediaProcessing did not stop within its timeout: [component name]"
为避免出现此异常,您可以执行以下任一操作:
- 让您的服务实现新的
Service.onTimeout(int, int)方法。当您的应用收到回调时,请务必在几秒钟内调用stopSelf()。(如果您未立即停止应用,系统会生成失败情况。) - 确保应用的
mediaProcessing服务在任何 24 小时内总运行时间不超过 6 小时(除非用户与应用互动,重置计时器)。 - 仅在有直接用户互动时启动
mediaProcessing前台服务;由于服务启动时应用位于前台,因此您的服务在应用进入后台后有完整的 6 小时时间。 - 请改用 替代 API(例如 WorkManager),而不是使用
mediaProcessing前台服务。
如果您的应用的 mediaProcessing 前台服务在过去 24 小时内运行了 6 小时,则您无法启动其他 mediaProcessing 前台服务,除非用户将您的应用切换到前台(这会重置计时器)。如果您尝试启动另一个 mediaProcessing 前台服务,系统会抛出 ForegroundServiceStartNotAllowedException,并显示类似于“前台服务类型 mediaProcessing 的时间限制已用尽”的错误消息。
如需详细了解 mediaProcessing 服务类型,请参阅 Android 15 前台服务类型变更:媒体处理。
测试
如需测试应用的行为,您可以启用媒体处理超时,即使您的应用并非以 Android 15 为目标平台也是如此(前提是应用在 Android 15 设备上运行)。如需启用超时,请运行以下 adb 命令:
adb shell am compat enable FGS_INTRODUCE_TIME_LIMITS your-package-name
您还可以调整超时期限,以便更轻松地测试应用在达到上限时的行为方式。如需设置新的超时期限,请运行以下 adb 命令:
adb shell device_config put activity_manager media_processing_fgs_timeout_duration duration-in-milliseconds
القيود المفروضة على تطبيقات BOOT_COMPLETED التي تستخدم مستقبلات البث لتشغيل الخدمات التي تعمل في المقدّمة
هناك قيود جديدة على إطلاق أجهزة استقبال بث BOOT_COMPLETED.
والخدمات التي تعمل في المقدّمة. لا يُسمح لأجهزة استقبال BOOT_COMPLETED بتشغيل
الأنواع التالية من الخدمات التي تعمل في المقدّمة:
dataSynccameramediaPlaybackphoneCallmediaProjectionmicrophone(تم فرض هذا التقييد علىmicrophoneمنذ بدء استخدام الإصدار 14 من نظام التشغيل Android)
إذا حاول مستقبل BOOT_COMPLETED بدء أيّ من هذه الأنواع من الخدمات التي تعمل في
المقدّمة، يُرسِل النظام الخطأ ForegroundServiceStartNotAllowedException.
الاختبار
لاختبار سلوك تطبيقك، يمكنك تفعيل هذه القيود الجديدة حتى إذا كان
تطبيقك لا يستهدف الإصدار 15 من Android (ما دام التطبيق يعمل على جهاز يعمل بالإصدار 15 من Android). شغِّل الأمر adb التالي:
adb shell am compat enable FGS_BOOT_COMPLETED_RESTRICTIONS your-package-name
لإرسال بث BOOT_COMPLETED بدون إعادة تشغيل الجهاز، يُرجى اتّباع الخطوات التالية:
شغِّل الأمر adb التالي:
adb shell am broadcast -a android.intent.action.BOOT_COMPLETED your-package-name
القيود المفروضة على بدء الخدمات التي تعمل في المقدّمة عندما يكون لدى التطبيق إذن SYSTEM_ALERT_WINDOW
في السابق، إذا كان التطبيق يمتلك إذن SYSTEM_ALERT_WINDOW، كان بإمكانه بدء
خدمة تعمل في المقدّمة حتى إذا كان التطبيق قيد التشغيل في الخلفية (كما هو описан في الاستثناءات من القيود المفروضة على بدء التطبيقات في الخلفية).
إذا كان التطبيق يستهدف الإصدار 15 من نظام التشغيل Android، أصبح هذا الإعفاء الآن أكثر تقييدًا. يجب أن يحصل التطبيق الآن على
إذن SYSTEM_ALERT_WINDOW وأيضًا أن يتضمّن نافذة ملف شخصي مثبّت
مرئية. وهذا يعني أنّ التطبيق يجب أن يفتح أولاً نافذة
TYPE_APPLICATION_OVERLAY و يجب أن تكون النافذة
مرئية قبل بدء خدمة تعمل في المقدّمة.
إذا حاول تطبيقك بدء خدمة تعمل في المقدّمة من الخلفية بدون
استيفاء هذه المتطلبات الجديدة (وليس لديه أي استثناء آخر)، يُرسِل
النظام الخطأ ForegroundServiceStartNotAllowedException.
إذا كان تطبيقك يعلن عن إذن SYSTEM_ALERT_WINDOW ويشغّل الخدمات التي تعمل في المقدّمة من الخلفية، قد يتأثّر بالتغيير الذي تم إجراؤه. إذا حصل تطبيقك على ForegroundServiceStartNotAllowedException، تحقَّق من
ترتيب عمليات تطبيقك وتأكَّد من أنّ تطبيقك لديه
نافذة تراكب نشطة قبل أن يحاول بدء خدمة تعمل في المقدّمة من
الخلفية. يمكنك التحقّق مما إذا كانت نافذة التراكب مرئية حاليًا
من خلال استدعاء View.getWindowVisibility()، أو
يمكنك إلغاء View.onWindowVisibilityChanged()
للحصول على إشعارات عند تغيير مستوى العرض.
الاختبار
لاختبار سلوك تطبيقك، يمكنك تفعيل هذه القيود الجديدة حتى إذا كان
تطبيقك لا يستهدف الإصدار 15 من نظام التشغيل Android (ما دام التطبيق يعمل على جهاز
Android 15). لتفعيل هذه القيود الجديدة على بدء الخدمات التي تعمل في المقدّمة
من الخلفية، شغِّل الأمر adb التالي:
adb shell am compat enable FGS_SAW_RESTRICTIONS your-package-name
تغييرات على الحالات التي يمكن فيها للتطبيقات تعديل الحالة العامة لوضع "عدم الإزعاج"
以 Android 15(API 级别 35)及更高版本为目标平台的应用无法再更改设备上的勿扰 (DND) 功能的全局状态或政策(无论是通过修改用户设置还是关闭勿扰模式)。相反,应用必须提供 AutomaticZenRule,系统会将其与现有的“最严格的政策优先”方案合并为一个全局政策。对之前会影响全局状态的现有 API 的调用(setInterruptionFilter、setNotificationPolicy)会导致创建或更新隐式 AutomaticZenRule,该 AutomaticZenRule 会根据这些 API 调用的调用周期开启和关闭。
请注意,只有当应用调用 setInterruptionFilter(INTERRUPTION_FILTER_ALL) 并希望该调用停用之前由其所有者激活的 AutomaticZenRule 时,此更改才会影响可观察到的行为。
تغييرات على واجهة برمجة تطبيقات OpenJDK
يواصل نظام التشغيل Android 15 عملية تحديث المكتبات الأساسية في Android لتتوافق مع الميزات المتوفّرة في أحدث إصدارات OpenJDK LTS.
يمكن أن تؤثّر بعض هذه التغييرات في توافق التطبيقات التي تستهدف الإصدار 15 من نظام التشغيل Android (المستوى 35 لواجهة برمجة التطبيقات):
تغييرات على واجهات برمجة التطبيقات الخاصة بتنسيق السلاسل: أصبح التحقّق من صحة فهرس الوسيطات والعلامات والعرض والدقة أكثر صرامة عند استخدام واجهتَي برمجة التطبيقات
String.format()وFormatter.format()التاليتَين:String.format(String, Object[])String.format(Locale, String, Object[])Formatter.format(String, Object[])Formatter.format(Locale, String, Object[])
على سبيل المثال، يتم طرح الاستثناء التالي عند استخدام فهرس وسيطة بقيمة 0 (
%0في سلسلة التنسيق):IllegalFormatArgumentIndexException: Illegal format argument index = 0في هذه الحالة، يمكن حلّ المشكلة باستخدام فهرس وسيطة بقيمة 1 (
%1في سلسلة التنسيق).تغييرات على نوع المكوّن في
Arrays.asList(...).toArray(): عند استخدامArrays.asList(...).toArray()، يصبح نوع المكوّن في المصفوفة الناتجةObject، وليس نوع عناصر المصفوفة الأساسية. لذلك، يعرض الرمز التالي الخطأClassCastException:String[] elements = (String[]) Arrays.asList("one", "two").toArray();في هذه الحالة، للحفاظ على
Stringكنوع المكوّن في المصفوفة الناتجة، يمكنك استخدامCollection.toArray(Object[])بدلاً من ذلك:String[] elements = Arrays.asList("two", "one").toArray(new String[0]);تغييرات على طريقة التعامل مع رموز اللغات: عند استخدام واجهة برمجة التطبيقات
Locale، لن يتم بعد الآن تحويل رموز اللغات العبرية واليديشية والإندونيسية إلى أشكالها القديمة (العبرية:iw، واليديشية:ji، والإندونيسية:in). عند تحديد رمز اللغة لإحدى هذه اللغات، استخدِم الرموز من معيار ISO 639-1 بدلاً من ذلك (العبرية:he، واليديشية:yi، والإندونيسية:id).التغييرات على تسلسلات الأعداد الصحيحة العشوائية: بعد التغييرات التي تم إجراؤها في https://bugs.openjdk.org/browse/JDK-8301574، أصبحت طرق
Random.ints()التالية تعرض تسلسلاً مختلفًا من الأرقام عن طرقRandom.nextInt():بشكل عام، من المفترض ألا يؤدي هذا التغيير إلى حدوث مشاكل في التطبيق، ولكن يجب ألا يتوقّع الرمز البرمجي أن يتطابق التسلسل الذي تم إنشاؤه من خلال طرق
Random.ints()معRandom.nextInt().
يمكن أن تؤثّر واجهة برمجة التطبيقات الجديدة SequencedCollection في توافق تطبيقك
بعد تعديل compileSdk في إعدادات التصميم في تطبيقك لاستخدام
الإصدار 15 من نظام التشغيل Android (المستوى 35 لواجهة برمجة التطبيقات):
تعارض مع وظائف الإضافات
MutableList.removeFirst()وMutableList.removeLast()فيkotlin-stdlibيتم ربط النوع
Listفي Java بالنوعMutableListفي Kotlin. بما أنّه تم طرح واجهتَي برمجة التطبيقاتList.removeFirst()وList.removeLast()في نظام التشغيل Android 15 (مستوى واجهة برمجة التطبيقات 35)، يحلّل برنامج التجميع في Kotlin استدعاءات الدوال، مثلlist.removeFirst()، بشكل ثابت إلى واجهات برمجة التطبيقات الجديدةListبدلاً من دوال الإضافة فيkotlin-stdlib.إذا تمت إعادة تجميع تطبيق مع ضبط
compileSdkعلى35وضبطminSdkعلى34أو إصدار أقدم، ثم تم تشغيل التطبيق على الإصدار 14 من نظام التشغيل Android أو إصدار أقدم، سيتم عرض خطأ وقت التشغيل:java.lang.NoSuchMethodError: No virtual method removeFirst()Ljava/lang/Object; in class Ljava/util/ArrayList;يمكن لخيار
NewApilint الحالي في المكوّن الإضافي لنظام Gradle المتوافق مع Android رصد حالات الاستخدام الجديدة لواجهات برمجة التطبيقات../gradlew lintMainActivity.kt:41: Error: Call requires API level 35 (current min is 34): java.util.List#removeFirst [NewApi] list.removeFirst()لحلّ خطأ وقت التشغيل وأخطاء Lint، يمكن استبدال استدعاءات الدالتَين
removeFirst()وremoveLast()بالدالتَينremoveAt(0)وremoveAt(list.lastIndex)على التوالي في Kotlin. إذا كنت تستخدم الإصدار 2024.1.3 من استوديو Android Ladybug أو إصدارًا أحدث، سيتوفّر لك أيضًا خيار إصلاح سريع لهذه الأخطاء.ننصحك بإزالة
@SuppressLint("NewApi")وlintOptions { disable 'NewApi' }إذا تم إيقاف خيار Lint.التعارض مع طرق أخرى في Java
تمت إضافة طرق جديدة إلى الأنواع الحالية، مثل
ListوDeque. قد لا تكون هذه الطرق الجديدة متوافقة مع الطرق التي تحمل الاسم نفسه وأنواع الوسيطات في الواجهات والفئات الأخرى. في حال حدوث تعارض في توقيع الطريقة مع عدم التوافق، سيُخرج برنامج التجميعjavacخطأ في وقت الإصدار. على سبيل المثال:مثال على الخطأ 1:
javac MyList.javaMyList.java:135: error: removeLast() in MyList cannot implement removeLast() in List public void removeLast() { ^ return type void is not compatible with Object where E is a type-variable: E extends Object declared in interface Listمثال على الخطأ 2:
javac MyList.javaMyList.java:7: error: types Deque<Object> and List<Object> are incompatible; public class MyList implements List<Object>, Deque<Object> { both define reversed(), but with unrelated return types 1 errorمثال على الخطأ 3:
javac MyList.javaMyList.java:43: error: types List<E#1> and MyInterface<E#2> are incompatible; public static class MyList implements List<Object>, MyInterface<Object> { class MyList inherits unrelated defaults for getFirst() from types List and MyInterface where E#1,E#2 are type-variables: E#1 extends Object declared in interface List E#2 extends Object declared in interface MyInterface 1 errorلإصلاح أخطاء الإصدار هذه، يجب أن تتجاوز الفئة التي تنفّذ هذه الواجهات الطريقة بنوع إرجاع متوافق. مثلاً:
@Override public Object getFirst() { return List.super.getFirst(); }
الأمان
يتضمّن Android 15 تغييرات تعزّز أمان النظام للمساعدة في حماية التطبيقات والمستخدمين من التطبيقات الضارّة.
إصدارات بروتوكول أمان طبقة النقل (TLS) المحظورة
Android 15 restricts the usage of TLS versions 1.0 and 1.1. These versions had previously been deprecated in Android, but are now disallowed for apps targeting Android 15.
عمليات إطلاق الأنشطة في الخلفية الآمنة
Android 15 做出了一些变更,可防止恶意后台应用将其他应用置于前台、提升自身权限并滥用用户互动,从而保护用户免受恶意应用的侵害,并让用户更好地控制自己的设备。自 Android 10(API 级别 29)起,后台 activity 启动受到限制。
其他更改
- 将
PendingIntent创建者更改为默认阻止后台活动启动。这有助于防止应用意外创建可能被恶意行为者滥用的PendingIntent。 - 除非
PendingIntent发送方允许,否则请勿将应用转至前台。此变更旨在防止恶意应用滥用在后台启动 activity 的功能。默认情况下,除非创建者允许后台 activity 启动权限或发送者具有后台 activity 启动权限,否则不允许应用将任务堆栈带到前台。 - 控制任务堆栈的顶层 activity 如何完成其任务。如果顶部 activity 完成了一项任务,Android 将返回到上次处于活跃状态的任务。此外,如果非顶部 activity 完成其任务,Android 会返回到主屏幕;它不会阻止此非顶部 activity 完成。
- 防止从其他应用启动任意 activity 进入您自己的任务。此变更可防止恶意应用通过创建看似来自其他应用的 activity 来对用户进行钓鱼式攻击。
- 阻止将非可见窗口纳入后台 activity 启动的考虑范围。这有助于防止恶意应用滥用后台活动启动来向用户显示不必要或恶意的内容。
الأهداف الأكثر أمانًا
يقدّم نظام التشغيل Android 15 StrictMode للأهداف.
للاطّلاع على سجلّات تفصيلية حول انتهاكات استخدام Intent، استخدِم الطريقة التالية:
Kotlin
fun onCreate() { StrictMode.setVmPolicy(VmPolicy.Builder() .detectUnsafeIntentLaunch() .build() ) }
Java
public void onCreate() { StrictMode.setVmPolicy(new VmPolicy.Builder() .detectUnsafeIntentLaunch() .build()); }
تجربة المستخدم وواجهة مستخدم النظام
يتضمّن Android 15 بعض التغييرات التي تهدف إلى إنشاء تجربة مستخدم أكثر اتساقًا وبديهية.
تغييرات على مساحة الحشو الداخلية للنافذة
هناك تغييران مرتبطان بزوايا النافذة في Android 15: يتم تطبيق التمويه من الحافة إلى الحافة تلقائيًا، وهناك أيضًا تغييرات في الإعدادات، مثل الإعدادات التلقائية لأشرطة النظام.
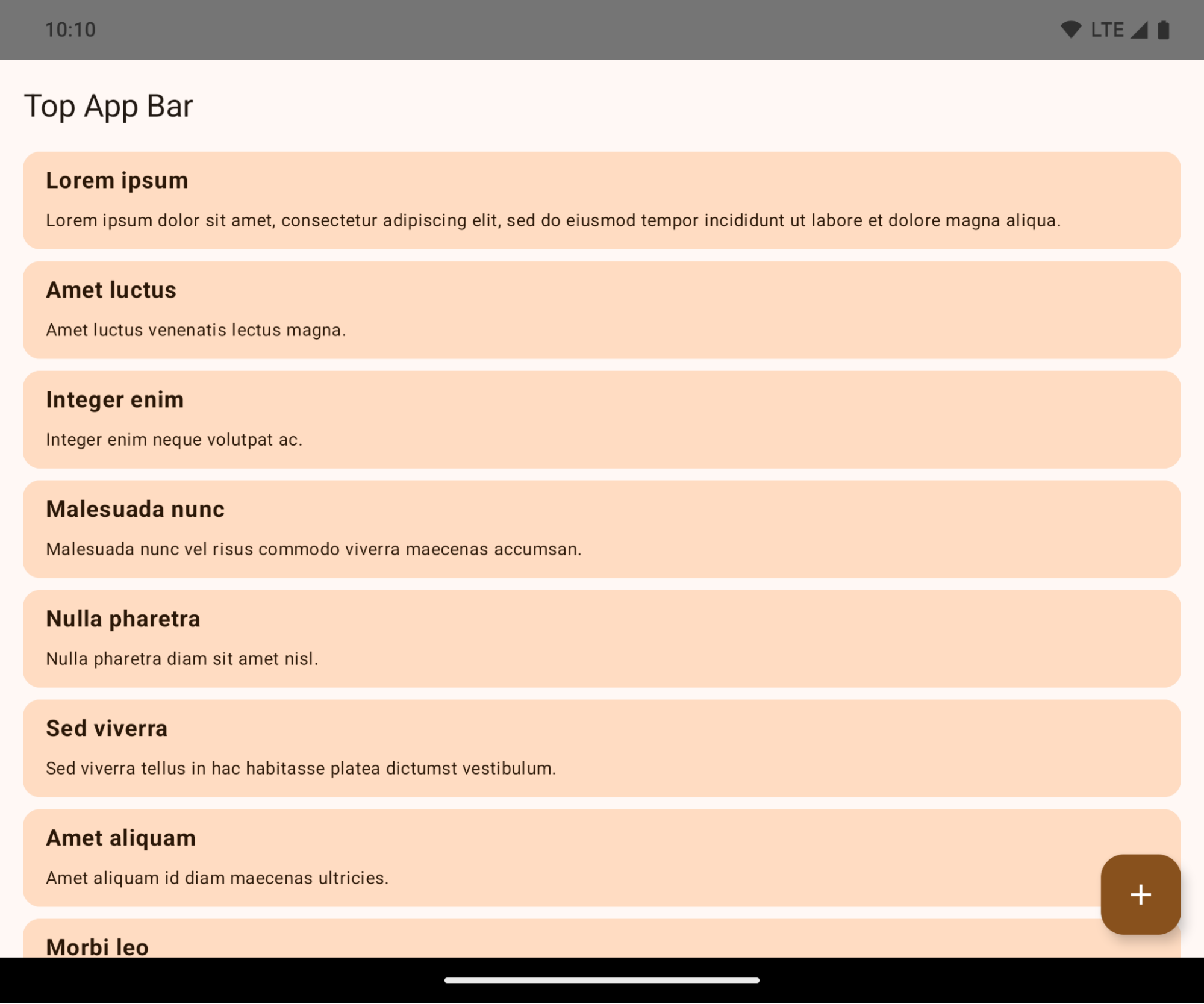
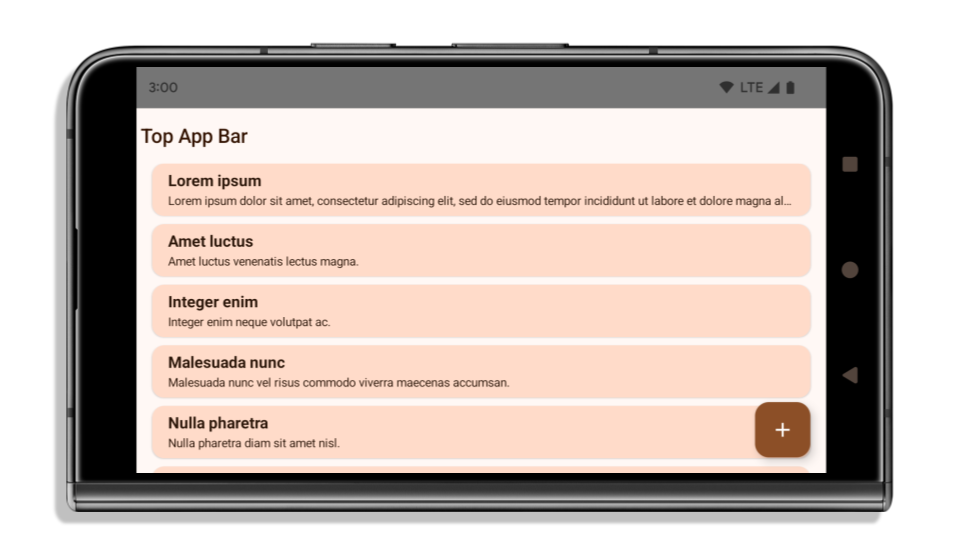
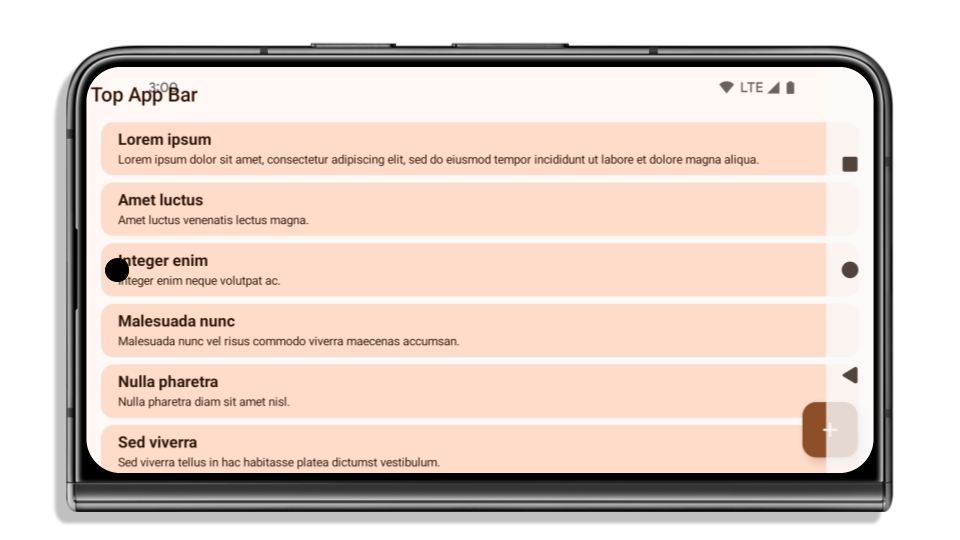
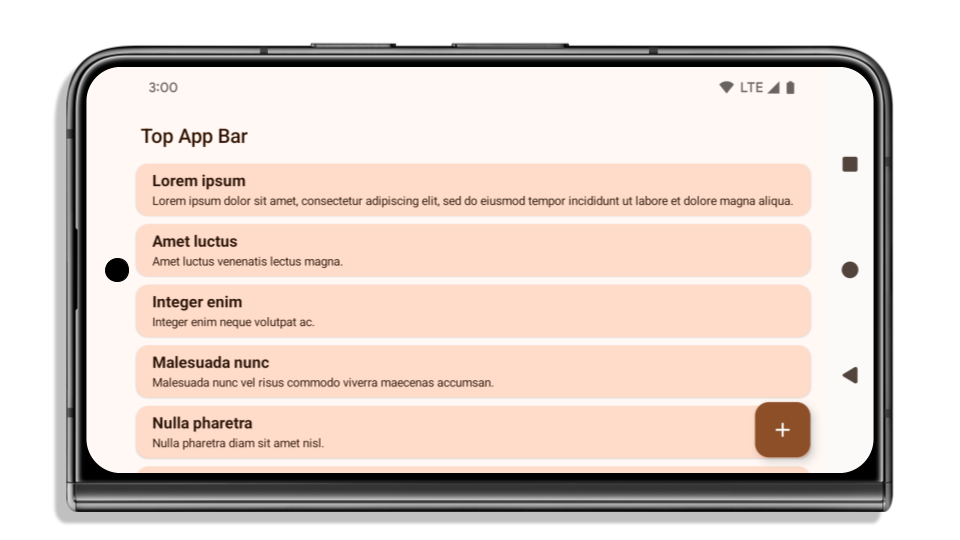
Edge-to-edge enforcement
如果应用以 Android 15(API 级别 35)为目标平台,则在搭载 Android 15 的设备上默认以无边框显示。
这是一项重大变更,可能会对应用的界面产生不利影响。这些变更会影响以下界面区域:
- 手势提示条导航栏
- 默认透明。
- 底部偏移已停用,因此除非应用了边衬区,否则内容会绘制在系统导航栏后面。
setNavigationBarColor和R.attr#navigationBarColor已弃用,不会影响手势导航。setNavigationBarContrastEnforced和R.attr#navigationBarContrastEnforced仍不会影响手势导航。
- 三按钮导航
- 默认情况下,不透明度设置为 80%,颜色可能与窗口背景颜色一致。
- 底部偏移已停用,因此除非应用了边衬区,否则内容会绘制在系统导航栏后面。
setNavigationBarColor和R.attr#navigationBarColor默认设置为与窗口背景颜色一致。窗口背景必须是颜色可绘制对象,才能应用此默认设置。此 API 已弃用,但仍会影响三按钮导航。setNavigationBarContrastEnforced和R.attr#navigationBarContrastEnforced默认值为 true,这会在三按钮导航中添加 80% 不透明的背景。
- 状态栏
- 默认透明。
- 顶部偏移已停用,因此除非应用了边衬区,否则内容会绘制在状态栏后面。
setStatusBarColor和R.attr#statusBarColor已弃用,不会影响 Android 15。setStatusBarContrastEnforced和R.attr#statusBarContrastEnforced已弃用,但仍会影响 Android 15。
- 刘海屏
- 非浮动窗口的
layoutInDisplayCutoutMode必须为LAYOUT_IN_DISPLAY_CUTOUT_MODE_ALWAYS。SHORT_EDGES、NEVER和DEFAULT会被解读为ALWAYS,这样用户就不会看到因显示屏刘海屏而产生的黑条,并且会以无边框显示。
- 非浮动窗口的
以下示例展示了应用在以 Android 15(API 级别 35)为目标平台之前和之后,以及在应用边衬区之前和之后的效果。此示例并不全面,在 Android Auto 上可能会显示不同的效果。
如果您的应用已以无边框显示,需要检查哪些内容
如果您的应用已以 无边框 显示并应用了边衬区,则大部分情况下 不会受到影响,但在以下情形中除外。不过,即使您认为自己不会受到影响,我们也建议您测试应用。
- 您有一个非浮动窗口,例如使用
SHORT_EDGES、NEVER或DEFAULT而不是LAYOUT_IN_DISPLAY_CUTOUT_MODE_ALWAYS的Activity。如果您的应用在启动时崩溃,可能是因为启动画面所致。您可以将 核心 启动画面 依赖项升级到 1.2.0-alpha01 或更高版本,也可以设置window.attributes.layoutInDisplayCutoutMode = WindowManager.LayoutInDisplayCutoutMode.always。 - 可能存在流量较低的屏幕,其界面被遮盖。验证这些访问量较少的屏幕是否没有被遮盖的界面。流量较低的屏幕包括:
- 新手入门或登录屏幕
- “设置”页面
如果您的应用尚未以无边框显示,需要检查哪些内容
如果您的应用尚未以无边框显示,则很可能会受到影响。除了已以无边框显示的应用的情形之外,您还应考虑以下情况:
- 如果您的应用在 Compose 中使用了 Material 3 组件 (
androidx.compose.material3),例如TopAppBar、BottomAppBar和NavigationBar,这些组件可能不会 受到影响,因为它们会自动处理边衬区。 - 如果应用使用的是 Compose 中的 Material 2 组件 (
androidx.compose.material),这些组件 本身并不会自动处理边衬区。不过,您可以获得边衬区的访问权限,然后手动应用边衬区。在 androidx.compose.material 1.6.0 及更高版本中,使用windowInsets参数可为BottomAppBar、TopAppBar、BottomNavigation和NavigationRail手动应用边衬区。 同样,对于Scaffold,请使用contentWindowInsets参数。 - 如果应用使用了视图和 Material 组件
(
com.google.android.material),则大多数基于视图的 Material 组件(例如BottomNavigationView、BottomAppBar、NavigationRailView或NavigationView)都会处理边衬区,因此不需要执行额外的操作。不过,您需要添加android:fitsSystemWindows="true",如果使用AppBarLayout。 - 对于自定义可组合项,请手动应用边衬区作为内边距。如果您的
内容位于
Scaffold中,则可以使用Scaffold内边距值来使用边衬区。否则,请使用其中一个WindowInsets应用内边距。 - 如果应用使用的是视图和
BottomSheet、SideSheet或自定义 容器,请使用ViewCompat.setOnApplyWindowInsetsListener应用内边距。对于RecyclerView,请使用此监听器应用内边距,同时添加clipToPadding="false"。
如果您的应用必须提供自定义背景保护,需要检查哪些内容
如果您的应用必须为“三按钮”导航或
状态栏提供自定义背景保护,则应用应使用 WindowInsets.Type#tappableElement() 将可组合函数或视图放置在系统栏后面
,以获取“三按钮”
导航栏高度或 WindowInsets.Type#statusBars。
其他无边框资源
如需了解有关应用边衬区的其他注意事项,请参阅无边框视图和无边框 Compose 指南。
已弃用的 API
以下 API 已弃用,但未停用:
R.attr#enforceStatusBarContrastR.attr#navigationBarColor(适用于三按钮导航,alpha 为 80%)Window#isStatusBarContrastEnforcedWindow#setNavigationBarColor(适用于三按钮导航,alpha 为 80%)Window#setStatusBarContrastEnforced
以下 API 已弃用并已停用:
R.attr#navigationBarColor(适用于手势导航)R.attr#navigationBarDividerColorR.attr#statusBarColorWindow#setDecorFitsSystemWindowsWindow#getNavigationBarColorWindow#getNavigationBarDividerColorWindow#getStatusBarColorWindow#setNavigationBarColor(适用于手势导航)Window#setNavigationBarDividerColorWindow#setStatusBarColor
Stable configuration
إذا كان تطبيقك يستهدف Android 15 (المستوى 35 لواجهة برمجة التطبيقات) أو الإصدارات الأحدث، لن يستبعد Configuration بعد الآن أشرطة النظام. إذا كنت تستخدم حجم الشاشة في فئة Configuration لاحتساب التنسيق، عليك استبداله ببدائل أفضل، مثل ViewGroup أو WindowInsets أو WindowMetricsCalculator مناسبة، حسب حاجتك.
تتوفّر فئة Configuration منذ المستوى 1 لواجهة برمجة التطبيقات. ويتم الحصول عليها عادةً من Activity.onConfigurationChanged. وتقدّم معلومات مثل كثافة النافذة واتجاهها وأحجامها. من الخصائص المهمة لأحجام النوافذ التي يتم عرضها من Configuration أنّها كانت تستبعد في السابق أشرطة النظام.
يُستخدَم حجم الإعدادات عادةً لاختيار الموارد، مثل /res/layout-h500dp، ولا تزال هذه حالة استخدام صالحة. ومع ذلك، لم ننصح أبدًا باستخدامه لاحتساب التنسيق. إذا كنت تستخدمه، عليك التوقّف عن ذلك الآن. عليك استبدال استخدام Configuration بشيء أكثر ملاءمةً حسب حالة الاستخدام.
إذا كنت تستخدمه لاحتساب التنسيق، استخدِم ViewGroup مناسبًا، مثل CoordinatorLayout أو ConstraintLayout. إذا كنت تستخدمه لتحديد ارتفاع شريط التنقّل في النظام، استخدِم WindowInsets. إذا أردت معرفة الحجم الحالي لنافذة تطبيقك، استخدِم computeCurrentWindowMetrics.
توضّح القائمة التالية الحقول المتأثّرة بهذا التغيير:
- لم يعُد حجمَا
Configuration.screenWidthDpوscreenHeightDpيستبعدان أشرطة النظام. Configuration.smallestScreenWidthDpيتأثّر بشكل غير مباشر بالتغييرات التي تطرأ علىscreenWidthDpوscreenHeightDp.Configuration.orientationيتأثّر بشكل غير مباشر بالتغييرات التي تطرأ علىscreenWidthDpوscreenHeightDpعلى الأجهزة القريبة من المربّع.Display.getSize(Point)يتأثّر بشكل غير مباشر بالتغييرات فيConfiguration. تم إيقاف هذه الطريقة نهائيًا بدءًا من المستوى 30 لواجهة برمجة التطبيقات.- تعمل
Display.getMetrics()بهذه الطريقة منذ المستوى 33 لواجهة برمجة التطبيقات.
القيمة التلقائية للسمة elegantTextHeight هي "صحيح"
对于以 Android 15(API 级别 35)为目标平台的应用,elegantTextHeight TextView 属性默认会变为 true,将默认使用的紧凑字体替换为一些具有较大垂直测量的脚本,使其更易于阅读。紧凑字体旨在防止布局中断;Android 13(API 级别 33)允许文本布局利用 fallbackLineSpacing 属性拉伸垂直高度,从而防止许多此类中断。
在 Android 15 中,系统中仍保留了紧凑字体,因此您的应用可以将 elegantTextHeight 设置为 false 以获得与之前相同的行为,但即将发布的版本不太可能支持此字体。因此,如果您的应用支持以下脚本:阿拉伯语、老挝语、缅甸语、泰米尔语、古吉拉特语、卡纳达语、马拉雅拉姆语、奥里亚语、泰卢固语或泰语,请将 elegantTextHeight 设置为 true 以测试您的应用。
elegantTextHeight 行为。
elegantTextHeight 行为。تغييرات على عرض TextView لأشكال الأحرف المعقّدة
在以前的 Android 版本中,某些具有复杂形状的手写字体或语言可能会在上一个或下一个字符的区域绘制字母。在某些情况下,此类字母会在开头或结尾处被剪裁。从 Android 15 开始,TextView 会分配宽度,以便为此类字母绘制足够的空间,并允许应用请求向左额外添加内边距以防止剪裁。
由于此更改会影响 TextView 确定宽度的方式,因此如果应用以 Android 15(API 级别 35)或更高版本为目标平台,TextView 会默认分配更多宽度。您可以通过对 TextView 调用 setUseBoundsForWidth API 来启用或停用此行为。
由于添加左内边距可能会导致现有布局未对齐,因此默认情况下不会添加内边距,即使以 Android 15 或更高版本为目标平台的应用也是如此。不过,您可以通过调用 setShiftDrawingOffsetForStartOverhang 添加额外的内边距以防止剪裁。
以下示例展示了这些更改如何改进某些字体和语言的文本布局。

<TextView android:fontFamily="cursive" android:text="java" />
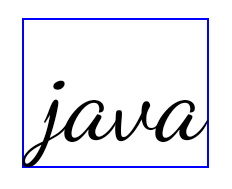
<TextView android:fontFamily="cursive" android:text="java" android:useBoundsForWidth="true" android:shiftDrawingOffsetForStartOverhang="true" />
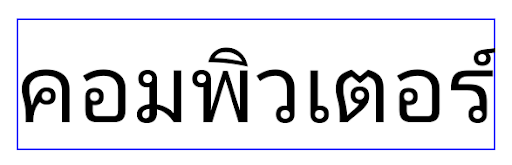
<TextView android:text="คอมพิวเตอร์" />
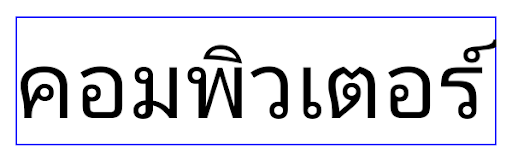
<TextView android:text="คอมพิวเตอร์" android:useBoundsForWidth="true" android:shiftDrawingOffsetForStartOverhang="true" />
ارتفاع السطر التلقائي الذي يراعي اللغة في EditText
في الإصدارات السابقة من Android، كان تنسيق النص يمدّد ارتفاع
النص ليتناسب مع ارتفاع سطر الخط الذي يتطابق مع اللغة الحالية. على سبيل المثال، إذا كان المحتوى باللغة اليابانية، يصبح ارتفاع النص أكبر قليلاً لأنّ ارتفاع السطر للخط الياباني
أكبر قليلاً من ارتفاع السطر للخط اللاتيني. ومع ذلك، على الرغم من هذه الاختلافات في ارتفاعات السطور، تم ضبط حجم العنصر
EditText بشكلٍ موحّد، بغض النظر عن
اللغة المستخدَمة، كما هو موضّح في الصورة التالية:
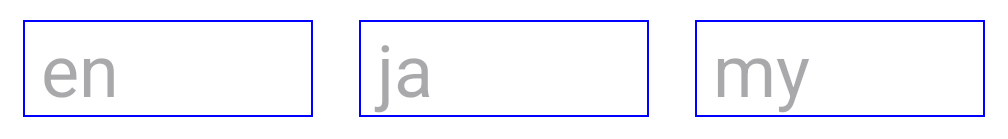
EditText عنصرًا يمكن أن يحتوي
على نص باللغة الإنجليزية (en) واليابانية (ja) والبورمية (my). يكون
ارتفاع الرمز EditText متطابقًا، على الرغم من أنّ هذه اللغات
لها ارتفاعات سطور مختلفة عن بعضها.بالنسبة إلى التطبيقات التي تستهدف الإصدار 15 من Android (المستوى 35 لواجهة برمجة التطبيقات)، تم الآن تخصيص الحد الأدنى لارتفاع السطر
لـ EditText لمطابقة الخط المرجعي للّغة المحدّدة، كما هو موضح
في الصورة التالية:

EditText عنصرًا يمكن أن يحتوي
على نص باللغة الإنجليزية (en) واليابانية (ja) والبورمية (my). يتضمّن الآن
ارتفاع الرمز EditText مساحة لاستيعاب
ارتفاع السطر التلقائي لخطوط هذه اللغات.يمكن لتطبيقك استعادة السلوك السابق إذا لزم الأمر من خلال تحديد سمة
useLocalePreferredLineHeightForMinimum
على false، ويمكن لتطبيقك ضبط الحد الأدنى المخصّص للمقاييس العمودية باستخدام واجهة برمجة التطبيقات
setMinimumFontMetrics في Kotlin وJava.
الكاميرا والوسائط
يُجري Android 15 التغييرات التالية على سلوك الكاميرا والوسائط للتطبيقات التي تستهدف Android 15 أو الإصدارات الأحدث.
القيود المفروضة على طلب أولويّة الصوت
يجب أن تكون التطبيقات التي تستهدف الإصدار 15 من نظام التشغيل Android (المستوى 35 لواجهة برمجة التطبيقات) هي التطبيق الأهم أو أن تعمل
بخدمة في المقدّمة من أجل طلب تركيز الصوت. إذا حاول أحد التطبيقات طلب التركيز عندما لا يستوفي أحد هذه المتطلبات، يعرض الإجراء AUDIOFOCUS_REQUEST_FAILED.
يمكنك الاطّلاع على مزيد من المعلومات حول ميزة "تركيز الصوت" في مقالة إدارة ميزة "تركيز الصوت".
القيود المعدَّلة على واجهات برمجة التطبيقات غير الأساسية في حزمة تطوير البرامج (SDK)
يتضمّن Android 15 قوائم معدَّلة لواجهات برمجة التطبيقات غير المتوفّرة في حزمة SDK والمقيّدة، استنادًا إلى التعاون مع مطوّري Android وأحدث الاختبارات الداخلية. نحرص قدر الإمكان على توفير بدائل عامة قبل تقييد واجهات برمجة التطبيقات غير المتوفّرة في حزمة SDK.
إذا كان تطبيقك لا يستهدف Android 15، قد لا تؤثّر بعض هذه التغييرات فيك على الفور. ومع ذلك، على الرغم من إمكانية وصول تطبيقك إلى بعض واجهات برمجة التطبيقات غير المتوفّرة في حزمة SDK استنادًا إلى مستوى واجهة برمجة التطبيقات المستهدَف في تطبيقك، فإنّ استخدام أي طريقة أو حقل غير متوفّر في حزمة SDK يحمل دائمًا خطرًا كبيرًا بتعطُّل تطبيقك.
إذا لم تكن متأكدًا مما إذا كان تطبيقك يستخدم واجهات برمجة تطبيقات غير متوفّرة في حزمة SDK، يمكنك اختباره لمعرفة ذلك. إذا كان تطبيقك يعتمد على واجهات برمجة تطبيقات غير متوفّرة في حزمة SDK، عليك البدء في التخطيط لنقل البيانات إلى بدائل حزمة SDK. ومع ذلك، ندرك أنّ بعض التطبيقات لديها حالات استخدام صالحة لاستخدام واجهات برمجة تطبيقات غير متوفّرة في حزمة SDK. إذا لم تتمكّن من العثور على بديل لاستخدام واجهة برمجة تطبيقات غير متوفّرة في حزمة SDK لميزة في تطبيقك، عليك طلب واجهة برمجة تطبيقات عامة جديدة.
لمزيد من المعلومات عن التغييرات في هذا الإصدار من Android، اطّلِع على التعديلات على قيود واجهات غير حزمة SDK في Android 15. للاطّلاع على مزيد من المعلومات حول الواجهات غير المتوفّرة في حزمة SDK بشكل عام، اطّلِع على مقالة القيود المفروضة على الواجهات غير المتوفّرة في حزمة SDK.

