Credential Manager 是建议用于 Android 应用中凭据交换的 Jetpack API。Credential Manager API 可简化各种设备规格的凭据交换,以用于身份验证和授权等使用情形。您还可以使用 Credential Manager 来处理数字凭据,并在新的 Android 设备上恢复用户凭据。
Credential Manager 功能
凭据管理器提供了一系列强大的功能,包括:
- 支持各种身份验证机制:使用户能够通过以下方式注册或登录您的应用:
- 通行密钥
- 使用 Google 账号登录和其他联合登录机制
- 密码
- 数字凭据
- 跨设备凭据恢复:与恢复凭据功能集成,让用户可以在新设备上顺畅地开始使用您的应用。
- 与凭据提供方无缝集成:支持凭据提供方,包括 Google 密码管理工具等密码管理工具。
- 凭据管理:支持更新用户凭据的元数据,有助于在应用和凭据提供方之间保持凭据一致。
- WebView 兼容性:可与使用 WebView 的应用搭配使用。
- 自动填充集成:与自动填充功能集成,以便在自动填充界面中显示凭据。
使用 Credential Manager 的好处
采用 Credential Manager 可为您的应用和用户带来多项关键优势:
- 增强型安全功能:通行密钥可增强安全性,并保护用户免遭钓鱼式攻击。
- 支持各种设备规格:这些 API 可在各种 Android 设备规格(包括移动设备、Android XR 设备和 Wear OS 设备)上运行。
- 简化了各种使用情形下的身份验证:数字凭证(例如数字驾照、公司 ID 和国民身份证)可在各种使用情形下进行身份验证,包括需要电话号码验证的使用情形。
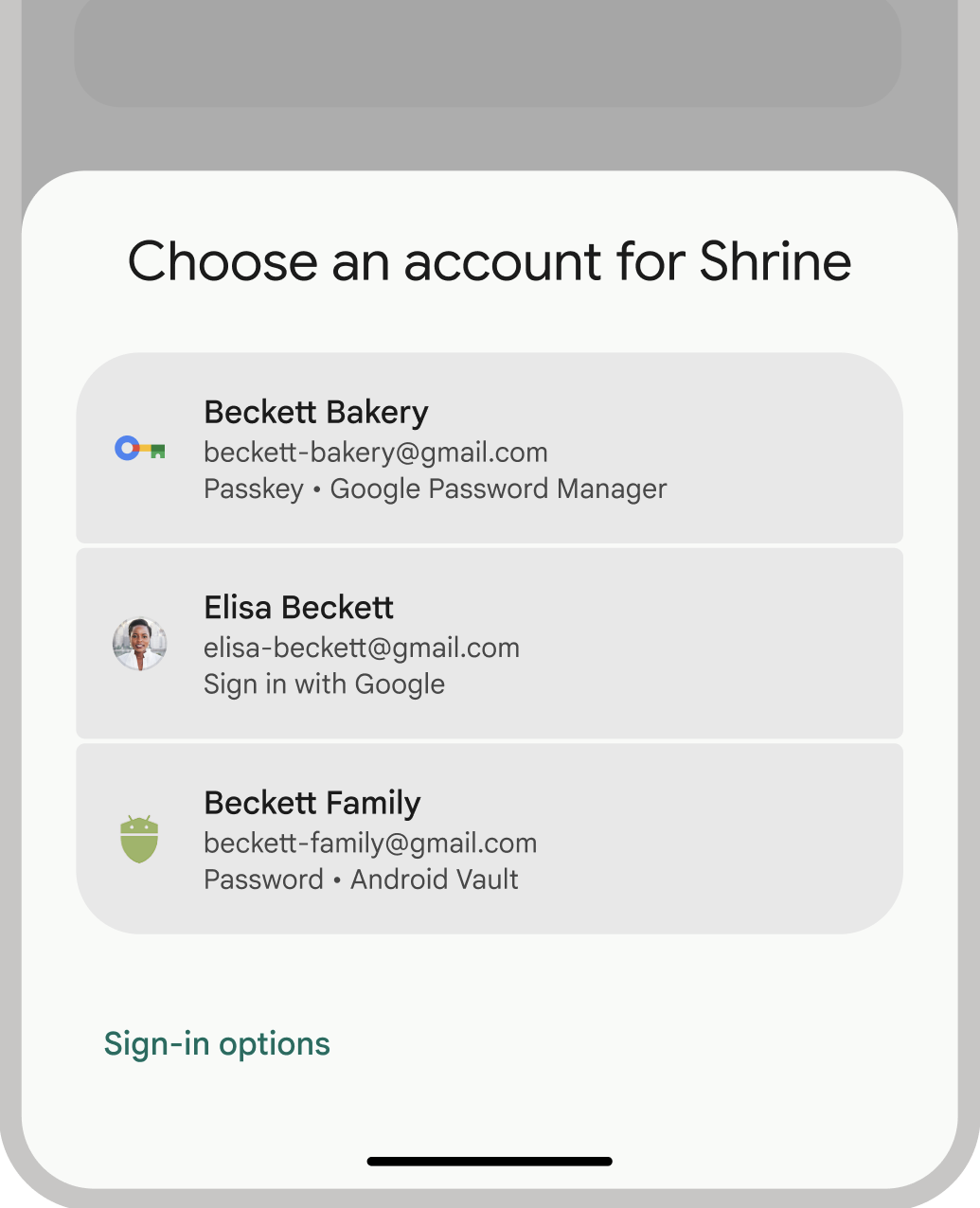
- 改善用户体验:Credential Manager 的统一界面可为用户提供熟悉且一致的体验,并提高注册和登录速度。底部工作表界面会与应用内容一起显示,因此用户在登录期间会一直停留在应用情境中。下图显示了凭据管理器的内置界面:
身份验证术语
要求用户进行身份验证的实体称为信赖方。身份验证工作流程通常包含以下组件:
- 信赖方客户端应用:处理用户界面以创建和使用通行密钥的客户端(在本例中为您的 Android 应用)。
- 信赖方服务器:一种应用服务器,可帮助创建、存储和验证通行密钥。
- 凭据提供程序:用于存储和提供用户凭据的组件,例如 Google 密码管理工具。请注意,FIDO 文档将凭据提供方称为凭据管理器。
凭据存储
凭据提供程序(例如 Google 密码管理工具)可为用户提供一个集中且安全的位置来管理其设备上的凭据,从而进一步简化身份验证流程。如需作为凭据提供程序与 Credential Manager 集成,请参阅将身份验证实现为凭据提供程序。
如需详细了解 Google 密码管理工具如何确保您的凭据安全,请参阅 Google 密码管理工具中通行密钥的安全性。
迁移到 Credential Manager
Credential Manager 旨在取代旧版 Android 身份验证 API 和本地 FIDO2 凭据。如需详细了解如何迁移到 Credential Manager,请参阅以下指南:
